The NIST Cybersecurity Framework is Powerful thinking tool for fighting Telecom Fraud
This article provides a guide you can use to lead a one-hour discussion to improve your ability to fight fraud in a Voice network.
What is the NIST CyberSecurity Framework (CSF)?
The CSF was developed by the US Federal Government to assist the government and private enterprise in developing their cybersecurity maturity. Many organizations use it as part of a thorough audit and assessment process to identify weak spots and prepare reports for their customers and partners.
Just because you can use the CSF as part of a large process, don't miss the usefulness as part of a quick, tactical conversation on specific types of vulnerabilities. As reported in February 2019 by Cloud Age Solutions, telecom fraud costs Service Providers billions of dollars per year -- between 1% and 2% of total revenue. That makes fraud -- especially on VoIP systems -- a major business issue.
Fraud is also a Cybersecurity issue; unfortunately, cybersecurity in the Voice space is remarkably weak: hence the $28 billion in loss each year.
Applying the Framework
The remainder of this article shows how you can leverage the CSF to target the specific, costly problem of telecom fraud. You can use these questions to drive your discussion and planning to have a discipline and effective approach.
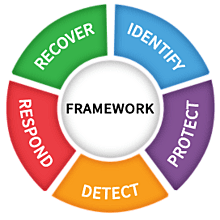
ID: Identify.
- What are the services through which calls can be made? Including:
- UCaaS - Hosted PBX - SIP Phones
- SIP Trunking
- Dial-in Voice portals
- Outdial from meet-me conferencing
- APIs, typically used for click-to-dial applications or Screen-Pops
- Call Forwarding / Redirection / Call Transfer
- Laws: What laws affect us here?
- Commonly, Rural Call Completion (RCC) rules can restrict your ability to block calls to certain high-cost destinations. Contact an attorney for exact details.
- Equipment and Services: What are the devices in our infrastructure that are involved in routing the fraudulent calls when they're made?
- Session Border Controllers
- Application Servers
- PSTN Gateways
PR: Protect
In general, it's best to protect against toll fraud to prevent it from happening in the first place -- and to minimize te dollars lost when it does happen. Much of the discussion about toll fraud focuses on this element, with good reason.
- What are the systems in place to protect our system against unauthorized use through the services we offer (UCaaS, SIP Trunking, Voice Portals, APIs, etc.)
- How are our SIP phones and others protected against spoofing (e.g., by stealing SIP credentials)?
- How are our web or app login portals protected?
- Do our customers know their responsibilities toward protection against fraud?
- How do we deactivate service for customers who cancel their service?
- How do we train & equip our personnel to ensure they don't assist bad actors in committing fraud (so called Social Engineering)?
- Are we applying all the best practices of cybersecurity -- including network segmentation, software updates, malware detection?
DE: Detect
Even with great protections in place, you need a backstop of detection. And detection must keep evolving with the attackers.
- Do we know what normal calling volumes look like to high cost destinations, and are we able to detect when volumes are improper?
- Are able to detect fraud events when the occur automatically?
- Are we testing our fraud-detection system to ensure it still functions properly?
- When a vendor detects fraud, who will they contact?
- Are we regularly improving our fraud detection processes to ensure they are keeping up with the attackers?
RS: Respond
Few organizations plan and discuss in advance what should happen when fraud is detected. But appropriate response -- including the mitigation -- can make a great difference in the dollars lost.
- Who is responsible for being aware of fraud incidents?
- What kind of reporting or communication should be happening when fraud occurs? (Is there any possibility that different departments are withholding information from one another?)
- Analysis: Are we analyzing how the fraud incident occurred and distributing what's discovered?
- Are we actively improving after problems occur in an organized, disciplined way?
- Mitigation: How do we stop the fraud event while it's ongoing?
- Are we reviewing the improvements through a change management process so that we're confident the changes are helpful and effective?
- Are there any scenarios where we need to contact others - like law enforcement or the FCC?
RC: Recover
- What's our process after a fraud incident occurs?
- With whom do we need to communicate after a fraud incident?